North Korean Crypto Wallet Sanctions Checker
Check Sanctioned Wallet Addresses
Enter a cryptocurrency wallet address to check if it's on the OFAC sanctions list for North Korean entities. The tool checks against publicly disclosed sanctioned wallet clusters.
Important note: This tool checks against publicly disclosed sanctioned wallet clusters from OFAC press releases. Some sanctioned addresses may remain hidden for operational security. Always verify with your compliance team and official OFAC resources.
When governments talk about North Korean crypto sanctions are a set of financial and legal measures aimed at cutting off the Democratic People’s Republic of Korea’s illicit crypto revenue streams, they’re really describing a high‑stakes cat‑and‑mouse game on the blockchain. The stakes are huge: the regime uses stolen digital assets to fund nuclear weapons and missile programs, while the rest of the world scrambles to block the money flow. Below is a clear, step‑by‑step look at how these sanctions work, which wallet addresses are on the watch list, and what you can do to stay compliant.
Why the sanctions exist and who enforces them
At the heart of the effort are United Nations Security Council Resolutions (UNSCRs). Since 2017, UNSCR 2375 and later resolutions have demanded that member states “freeze, confiscate, or otherwise prevent the transfer of funds that could support the DPRK’s weapons programs.” The U.S. Treasury’s Office of Foreign Assets Control (OFAC) translates those UN mandates into concrete designations - adding individuals, companies, and even blockchain addresses to its Specially Designated Nationals (SDN) list.
Since July 2025, OFAC has sanctioned more than a dozen entities tied to crypto‑related fraud schemes, such as Vitaliy Sergeyevich Andreyev and the Korean firm Shenyang Geumpungri Network Technology Co., Ltd. Each sanction comes with a public notice that lists known wallet clusters, giving banks and exchanges a reference point for screening.
Recent sanction actions and the wallet clusters they target
The latest wave of designations focuses on the “IT‑worker” scheme the DPRK runs abroad - a network of hackers, money‑launderers, and front companies that siphon crypto and sell it for fiat. Below is a snapshot of the most significant sanctions announced in 2025:
| Entity / Individual | Date | Reason | Known Wallet Cluster |
|---|---|---|---|
| Kim Ung Sun | July 24, 2025 | Fraudulent IT‑worker scheme, crypto theft | 0xA1…F3B2 |
| Shenyang Geumpungri Network Technology Co., Ltd. | July 24, 2025 | Facilitating sanctions evasion via crypto mixers | 0x4C2…9E7D |
| Korea Sinjin Trading Corporation | July 24, 2025 | Export of illicit cryptocurrency to fund missile program | 0xD8E…2A1C |
Note that public reports often hide the full address list to protect ongoing investigations. However, the clusters shown here are the ones most exchanges now flag in real time.
How blockchain analytics firms pinpoint DPRK wallets
Companies like Elliptic blend on‑chain data with intelligence from law‑enforcement partners. Their toolbox includes:
- Transaction pattern recognition - spotting repeated use of “tumbling” services that match known DPRK laundering signatures.
- Cluster analysis - grouping addresses that interact heavily with each other and with sanctioned wallets.
- Cross‑chain tracing - following assets as they hop from Bitcoin to Ethereum, then to privacy coins such as Monero.
In October 2025, Elliptic reported that DPRK actors stole $2.03 billion in crypto this year, a record driven largely by the $1.46 billion Bybit breach in February. Their analysis also unveiled more than thirty‑four additional hacks that bore the hallmarks of North Korean activity, though many lacked enough evidence for a firm attribution.
Big hacks of 2025: The Bybit case and beyond
The February Bybit incident remains the headline‑grabbing example of DPRK’s scale. Hackers exploited a vulnerability in the exchange’s hot‑wallet management, siphoning $1.46 billion worth of Bitcoin, Ethereum, and stablecoins. After the theft, the funds were quickly funneled through a series of mixers, then split into smaller batches that landed in the wallet clusters listed above.
Other notable targets include:
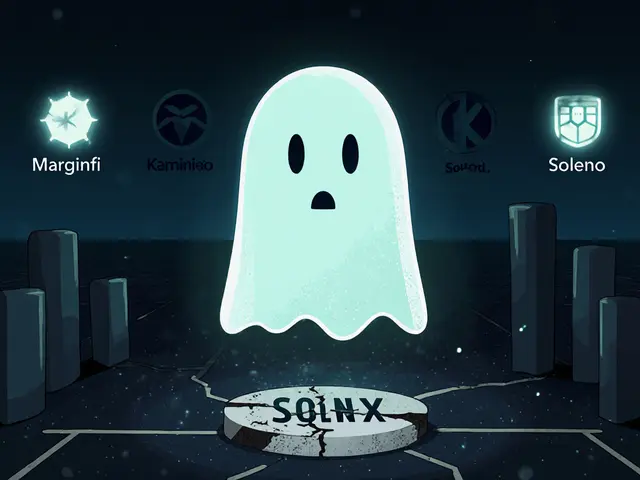
- LND.fi - a DeFi liquidity platform hit for $210 million.
- WOO X - suffered a $180 million loss in a coordinated phishing campaign.
- Seedify - a launchpad whose token sale proceeds were partially diverted.
These attacks illustrate a pattern: the DPRK first gains access to a centralized service, then uses sophisticated laundering chains to obfuscate the origin before moving the crypto into its own off‑shore accounts.
Why wallet‑level sanctions are hard to enforce
Unlike traditional bank accounts, crypto wallets are pseudonymous and can be spun up instantly. The DPRK counters sanctions in three main ways:
- Mixing services - platforms that pool together many users’ coins and re‑issue them, breaking the link between source and destination.
- Cross‑chain swaps - moving assets from Bitcoin to privacy‑focused chains like Monero, then back to a fiat‑compatible coin.
- Layer‑2 solutions - using networks such as Lightning or Optimism to fragment transactions into micro‑payments that slip past basic monitoring tools.
Because each hop erodes the trail, regulators rely heavily on advanced analytics and on‑chain intelligence sharing across borders. The Multilateral Sanctions Monitoring Team (MSMT) coordinates 11 nations to collect, verify, and publish evidence of violations, but the sheer volume of blockchain data makes real‑time enforcement a moving target.
Practical steps for financial institutions and crypto businesses
If you run a compliance program, here’s a checklist to stay ahead of DPRK‑related risks:
- Integrate a blockchain‑monitoring solution that flags transactions involving known DPRK wallet clusters.
- Adopt a risk‑based approach: higher‑value transactions (> $100,000) trigger deeper on‑chain investigation.
- Maintain an updated OFAC SDN list and cross‑reference it with the wallet clusters published in Treasury press releases.
- Train AML analysts on the specific laundering patterns DPRK actors use (e.g., rapid multi‑hop swaps, use of privacy coins).
- Participate in information‑sharing forums hosted by the MSMT or the Financial Action Task Force (FATF) to receive timely alerts.
Remember, sanctions compliance isn’t a one‑off check. The DPRK regularly adapts its techniques, so continuous monitoring and periodic rule‑set updates are essential.
Looking ahead: DeFi, bridges, and the next wave of threats
Analysts at Elliptic forecast that by 2026 the DPRK will target decentralized finance protocols and cross‑chain bridges more aggressively. These infrastructures are attractive because they often lack KYC checks and move large sums with minimal friction.
Two emerging trends could shape the next chapter:
- Automated smart‑contract exploits - bots that drain liquidity pools in seconds, then route the proceeds through mixers.
- Cross‑chain bridge attacks - hijacking the asset‑wrapping process to mint counterfeit tokens that can be moved off‑chain.
Governments are already responding. In late 2025, the U.S. Treasury announced a “whole‑of‑government” effort that includes a $15 million reward for tips leading to the disruption of DPRK crypto operations. Combined with the MSMT’s expanding network of national experts, the pressure on the regime’s illicit finance engine is mounting, but the cat‑and‑mouse game will likely continue for years.
Key takeaways
- North Korean crypto sanctions target the regime’s primary funding source for weapons development.
- Sanctioned wallet clusters are publicly listed in OFAC notices, but many remain hidden for operational security.
- Blockchain analytics firms like Elliptic use pattern‑recognition, clustering, and cross‑chain tracing to identify DPRK activity.
- Financial institutions must adopt advanced on‑chain monitoring and stay updated on sanction lists to avoid violations.
- The next threat wave will focus on DeFi and bridges, demanding even tighter surveillance.
What are the main sanctions imposed on North Korean crypto actors?
The sanctions mainly come from UN Security Council resolutions and U.S. OFAC designations. They freeze assets, ban transactions with listed individuals, companies, and specific blockchain wallet clusters linked to the DPRK’s illicit activities.
How can exchanges detect sanctioned DPRK wallets?
By integrating blockchain‑monitoring tools that reference the latest OFAC SDN lists and the wallet clusters disclosed in Treasury press releases. Real‑time alerts for transactions that touch these addresses are essential.
Why does the DPRK use mixers and privacy coins?
Mixers break the transaction trail by pooling many users’ coins, while privacy coins such as Monero hide sender and receiver details. Both techniques make it harder for analysts to trace stolen funds back to the regime.
What recent hack highlighted the scale of DPRK crypto theft?
The February 2025 breach of the cryptocurrency exchange Bybit, where $1.46 billion was stolen, became the single largest crypto theft attributed to North Korean actors in a single incident.
What steps should a compliance team take today?
Start by updating OFAC sanction lists, deploy a blockchain analytics solution that flags DPRK wallet clusters, train analysts on laundering patterns, and join multinational information‑sharing groups like the MSMT.


Comments (13)